Fairfyproof’s Analysis of Challenges Presented by Ransomware
Recently, FinCEN released a report titled “Ransomware Trends in Bank Secrecy Act Data Between January 2021 and June 2021”. which analyzes…
Recently, FinCEN released a report titled “Ransomware Trends in Bank Secrecy Act Data Between January 2021 and June 2021”. which analyzes trends, development, and patterns pertaining to ransomware in the first half of 2021.
The report says, “The total U.S. dollar value for ransomware-related transactions reported in SARs filed during the review period exceeds that of any previous year since 2011.”
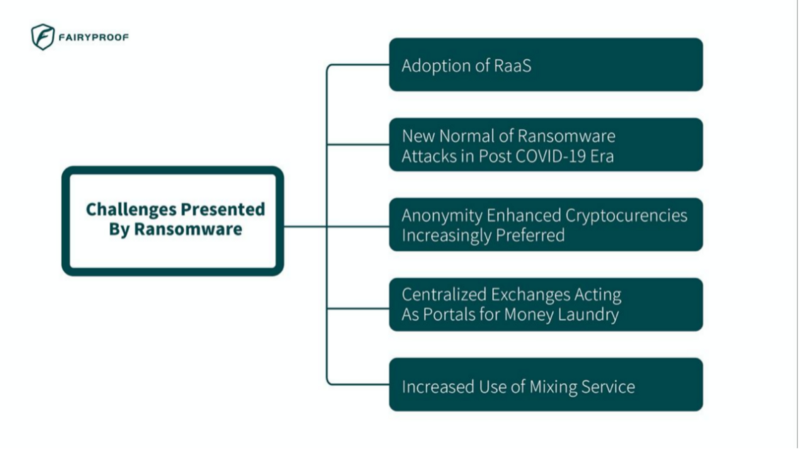
This statistic presents significant challenges presented by ransomware attacks that security companies must face and handle.
1. Adoption of Ransomware-as-a-service (RaaS)
“Some ransomware actors have diversified their revenue streams using a ransomware-as-a-service (RaaS) business model in which ransomware creators sell user-friendly ransomware kits on the Dark Web or outsource ransomware distribution to affiliates in exchange for a percentage of the ransom.”
RaaS is a relatively new business model for ransomware developers. In this model ransomware, developers sell or lease their ransomware to others (“affiliates”) who then use them to launch cyber attacks.
RaaS greatly lowers the technical expertise needed to launch attacks and makes cyber attacks much easier and more frequent therefore in recent years using RaaS to carry out attacks has been increasingly popular in cyberspace.
In order to recruit as many affiliates as possible, ransomware developers usually post queries on the dark web which is hard to trace and track. This throws a big challenge for security companies to promptly deliver solutions to protect applications from being attacked by ransomware or help recover ransomware-attacked applications.
2. New Normal of Ransomware Attacks in Post COVID-19 Era
“The transition to remote and online work in response to COVID-19 has also exacerbated risks and vulnerabilities of businesses to cyber attacks such as ransomware. Attacks on small municipalities and healthcare organizations have also increased, typically due to perceived weaker security controls and the higher propensity of these victims to pay the ransom because of the criticality of their services, particularly during a global health pandemic.”
The COVID-19 pandemic has fundamentally changed our everyday life. Besides entertainment and social activities on the internet, in the post-COVID-19 era, people’s work, dining, and many more become increasingly reliant on the internet as well and people spend much more time and do more online activities than in the real world.
This is a new normal in the post-COVID-19 era and this “new normal” is and will exacerbate risks and vulnerabilities of our daily activities to ransomware attacks.
In addition, the victims that ransomware attacks target spread from governments to businesses such as energy infrastructures, healthcare organizations, etc.
This is a strong warning that today companies that play critical roles in people’s daily life and have online services or activities but didn’t pay much attention to cyber security should be urged to take actions to prevent ransomware. This new normal also urges security companies to push technical boundaries and deliver more effective and efficient solutions to handle ransomware attacks
3. Anonymity Enhanced Cryptocurrencies Increasingly Preferred
“FinCEN identified BTC as the most common ransomware-related payment method in reported transactions. FinCEN also observed that incidents requesting Monero (XMR), an AEC, is on track to increase slightly compared to 2020.”
Although the payment requests in AEC in the first half of 2021 were just slightly higher than 2020 according to the report, we believer this trend will continue and grow much faster than expected since AEC has superior anonymous and anti-censorship features than Bitcoin.
Receiving payments in AEC is the best way to protect a receiver’s identity. This will very likely be adopted by more ransomware attackers.
Tracking and tracing AECs is one of the biggest challenges to the whole blockchain security industry. So far it is still technically not easy to track and trace some AECs such as Monero.
4. Centralized Exchanges Acting As Portals for Money Laundry
“Non-compliant centralized exchanges are possibly a key step in the layering and obfuscation process of laundering funds from CVC to fiat currency.”
The report pointed out that centralized exchanges especially those that are not KYC compliant play a vital role for ransomware attackers to cash out their ransoms.
Those non-compliant exchanges are usually wild and not regulated by any government.
This adds barriers to monitoring their transactions.
5. Increased Use of Mixing Service
“FinCEN observed an increased use of mixing services in SARs.”
“Cryptocurrency mixing service is a service to mix potentially identifiable or ‘tainted’ cryptocurrency funds with others, so as to obscure the trail back to the fund’s original source.”
There are some popular mixing service DApps such as Tornado Cash which is frequently used to mix ETH payments and may further extend its service to other crypto tokens as well.
A mixing service DApp achieves anonymity by using technologies such as zero-knowledge proofs, funding pooling, etc. It is difficult to trace exact transactions after they are sent to it.
In this article, we elaborated on 5 challenges. There are some other challenges mentioned in the report as well and even more, challenges are underway.
As people increasingly rely on the internet and the adoption of cryptocurrencies becomes drastically popular, ransomware attacks will take place more frequently and victims will get hurt more severely. To tackle these challenges presented by ransomware will be a long-lasting battle that security companies need to put long-term efforts and resources in.
About the author:
Yuefei TAN, CEO of Fairyproof
About Fairyproof:
Fairyproof Tech is a blockchain security company, established in Jan 2021.
It was founded by a team with rich experience in smart contract programming and network security. The team members participated in initiating a number of draft standards in the Ethereum field, including ERC-1646, ERC-2569, ERC-2794, and EIP-3712, of which ERC-2569 was officially accepted by the Ethereum team.
The team participated in the launch and development of various Ethereum projects, including blockchain platforms, DAO organizations, on-chain data storage, decentralized exchanges, and conducted security audits of multiple projects which have been deployed on Ethereum. Based on its strong R&D capability and deep understanding of smart contract security, Fairyproof has developed comprehensive vulnerability tracking and security systems and tools.
Fairyproof Tech serves and works closely with customers by providing systematic solutions covering both “code vulnerabilities” and “logic vulnerabilities” and aims to provide customers with the best and most professional services.