Fairyproof’s Overview of the Audit of the GameFi Ecosystem
Blockchain games have a relatively long history compared to other applications such as DeFi in the whole blockchain ecosystem.
Blockchain games have a relatively long history compared to other applications such as DeFi in the whole blockchain ecosystem.
CryptoKitties[1] which may be the earliest blockchain game was deployed and released in 2017 and it opened the infinite possibilities for blockchain games. However, blockchain games didn’t see their rapid development or gain significant traction until Axie Infinity [2] became popular in Southeast Asia with strong promotion from YGG [3] since 2020. A significant reason why Axie Infinity could grow its user base rapidly was that it introduced DeFi into its game. The success story of Axie Infinity encouraged numerous developers and teams to enter the blockchain game area and follow its example or provide services pertaining to blockchain games that have in-built DeFi mechanisms. This combination of games and DeFi was later on called GameFi.
Although the blockchain GameFi ecosystem has achieved tremendous progress, neither has research on the ecosystem’s security in academies gained sufficient awareness nor have comprehensive practices in tackling the security issues or risks been carefully carried out or studied.
Based on the accumulated experiences and research results from Fairyproof’s technical team in years’ practice, Fairyproof would like to share some understanding and thoughts on the overall blockchain GameFi ecosystem and the audit of the applications in this ecosystem.
In this paper, we firstly present our understanding of the overall blockchain GameFi ecosystem, analyze the applications, and the roles and functions these applications play; then present the applications’ underlying technologies and list typical security issues or risks associated with the underlying technologies; and finally present our ideas and thoughts about the audit of each of these applications.
1. Overview of the Blockchain GameFi Ecosystem
Currently, although the blockchain GameFi ecosystem may not be as mature as some experts would expect, it is already an ecosystem with various players, roles, applications, services, etc. that are rapidly growing and developing.
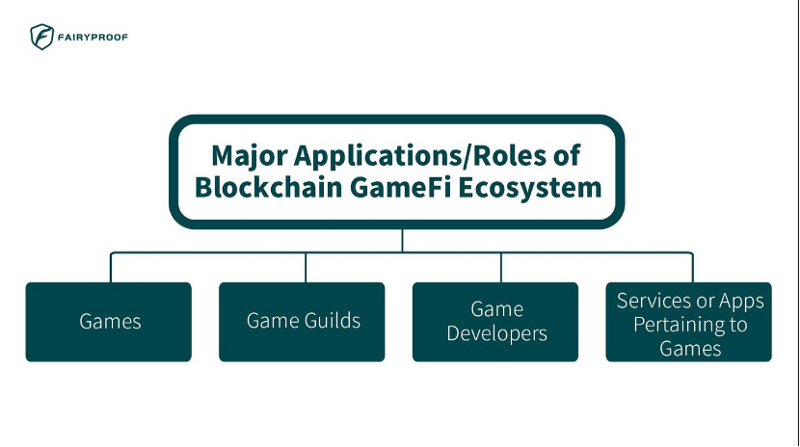
Typical applications/roles in the current blockchain GameFi ecosystem mainly consist of games, game guilds [4], game developers, services, or applications pertaining to games.
Games in this ecosystem are applications that mainly implement play rules and logic. Users/players directly interact with games. From an application’s point of view, games are the core component of the GameFi ecosystem. CryptoKitties and Axie Infinity are typical blockchain games.
Game guilds are a special player in this ecosystem. Popular blockchain games in general have an in-built play-to-earn mechanism that rewards tokens to its players. To earn rewards, a player may need to use in-game utilities which may not be affordable to every player. In this case, a game guild comes to play. It is an organization that acts as a facilitating intermediary to help hundreds or thousands or even more players play and earn yields in blockchain games by lending these players in-game assets or utilities. A guild will usually take profits by sharing a portion of the earnings earned by the players that rely on its help and the rent paid by the players that borrow in-game utilities or assets from the guild. YGG is the most famous blockchain game guild.
Game developers here don’t mean individuals but organizations, teams, or even DAOs (Decentralized Autonomous Organizations) [5] that develop games, services, or applications pertaining to games. Some famous game developers include SkyMarvis[6], Vulcan Verse[7], etc.
Services or applications pertaining to games refer to those that help grow and develop games’ user bases or help games evolve. Typical services or applications include marketplace applications such as OpenSea[8] and SkyMarvis’ marketplace[9], and asset or utility lending applications such as NFTFI[10].
2. Blockchain GameFi Ecosystem’s Underlying Technologies and Associated Issues or Risks
If we review these applications/roles listed in the previous section from a technical point of view and study their underlying technical standards or protocols, the whole blockchain GameFi ecosystem can be depicted as follows:
The top layer is what we call an application layer that contains the major applications/roles in the ecosystem. The underlying layer is what we call an infrastructure layer that contains two kinds of technologies: web 2.0 technologies/protocols and decentralized technologies/protocols. These two interact with each other via RPC calls.
The web 2.0 technologies/protocols can be viewed as being composed of two sub-layers: the sub-layer of C/S infrastructure, and the sub-layer of application UIs and backend services that run on the C/S infrastructure.
A UI (user interface) is the front-end of an application. When a user interacts with an application, he/she directly interacts with its UI.
Backend services execute functions based on the requests sent from UIs and respond to UIs with results and feedback.
The decentralized technologies/protocols can be viewed as being composed of three sub-layers:
the bottom sub-layer is an infrastructure layer which contains blockchain infrastructure, decentralized storage protocols such as IPFS [11] and Arweave [12], and other decentralized protocols.
The one on top of the blockchain infrastructure is the token sub-layer which contains fungible tokens and non-fungible tokens implemented based on various token standards.
The one that relies on the token layer, the blockchain infrastructure, the decentralized storage protocols, and other decentralized protocols is the utility/asset sub-layer which contains tokenomics, governance, in-game assets or utilities, and implementation of on-chain logic, data storage solutions, and other solutions/services. This layer provides various utility or functional building blocks for all the applications that users interact with.
3. Typical Issues or Risks Associated with The Components in The Infrastructure Layer
When we review the security condition of an application, we first need to study how the application works and what technologies or protocols are applied to make it work and then analyze what issues or risks might be introduced when these technologies or protocols are applied.
So, in this section, we review in general what typical issues or risks are associated with each of the components in the infrastructure layer.
3.1 Web 2.0 Technologies/Protocols
C/S Infrastructure: this refers to commonly used utilities, tools, and various network protocols. This is the infrastructure that all internet applications or conventional software applications rely on.
Professionals from around the globe have been working on this for a long time and overall, it has been pretty much mature so far. Occasionally bugs or vulnerabilities pertaining to it would be reported and bug fixes would be promptly released as well.
So, when we audit an application, we don’t usually audit this component but would check if the application has already been updated with the latest patches that are released for newly uncovered vulnerabilities or bugs.
UIs: a UI is what a user directly interacts with when the user interacts with an application. Therefore, if an application’s UI has vulnerabilities, its users would be easily exploited. Hackers have developed various ways to exploit vulnerabilities to attack UIs.
Typical vulnerabilities pertaining to UIs are including XSS attacks, CSRF attacks, CSS injection attacks, session hijacking, using unsafe third-party libraries, DDoS attacks, feature requests or access, etc.
Backend Services: in general, the backend service of an application processes requests sent by the application’s UI and returns the result to the UI.
With regard to a blockchain application, besides the commonly known communication between the backend and the UI, there is communication between the backend and a blockchain as well. Therefore, a security company needs to audit specifically the security condition of the latter as well. This somehow might be overlooked.
Typical vulnerabilities pertaining to backend services of blockchain applications are injection flaws, broken authentication, compromised access control, data breaches, insecure deserialization, server XSS attacks, etc.
3.2 Decentralized Technologies/Protocols
Blockchain Infrastructure: this refers to blockchains including layer 1 blockchains, layer 2 solutions, and sidechains. The blockchain infrastructure provides the fundamental security and consensus of the whole blockchain GameFi ecosystem. Therefore, its security condition is vital to the whole ecosystem.
Among the existing blockchains, some such as Ethereum have endured challenges but most of them were just online in the past two years and haven’t endured enough challenges. Thus, the security condition of these less mature blockchains needs our great awareness.
Typical vulnerabilities pertaining to blockchain infrastructure are 51% attacks, DDoS attacks, Sybil attacks, double-spend, race attacks, eclipse attacks, routing attacks, replay attacks, etc.
Decentralized Storage Protocols (IPFS, Arweave …): this refers to the protocols that are specifically used for storage in the GameFi ecosystem. The most popular protocols include IPFS and Arweave.
Typical vulnerabilities pertaining to decentralized storage protocols are DDoS attacks, Sybil attacks, etc.
Other decentralized protocols: these are protocols that may be introduced in the future. So, for now, no specific vulnerabilities are listed here.
Fungible Tokens: most of the fungible tokens today are implemented based on Ethereum’s ERC-20[13] standard. Some tokens are implemented based on Solana’s [14] token templates. Issues or risks related to fungible tokens are mostly in the tokens’ smart contract implementation.
Specifically for ERC-20 tokens, typical vulnerabilities are re-entrancy attacks, excessive admin rights, integer overflow/underflow, gas consumption issues, inappropriate callback, inappropriate function visibility, inappropriate arithmetic precision, and incorrect using tx. origin, fake deposit, shadow variable, token issuance issue, inappropriate proxy design, inappropriate use of slots, contract upgrade/migration issue, etc.
For fungible tokens implemented on Solana, typical vulnerabilities are missing ownership checks, missing signer checks, signed invocation of unverified programs, Solana account confusions, missing freeze authority checks, insufficient SPL account verification, missing rent exemption assertion, casting truncation, arithmetic overflow/underflow, numerical precision errors, instructions account checks, rug pull mechanisms or hidden backdoor checks, outdated dependencies, none returned during any failure, unreferenced accounts checks, serialize and deserialize checks, account address checks, unaudited external dependencies, program upgrade checks, account mutable checks, etc.
Non-Fungible Tokens: most of the non-fungible tokens are implemented based on Ethereum’s ERC-721[15] or ERC-1155[16] standard. Some tokens are implemented based on Solana’s token templates. Issues or risks related to non-fungible tokens are mostly in the tokens’ smart contract implementation.
For ERC-721 or ERC-1155 tokens, typical vulnerabilities are re-entrancy attacks, excessive admin rights, integer overflow/underflow, incorrect nonce values, gas consumption issues, inappropriate callback, inappropriate function visibility, incorrect using tx. origin, fake deposit, shadow variable, token issuance issue, inappropriate proxy design, inappropriate use of slots, contract upgrade/migration issue, etc.
For non-fungible tokens implemented on Solana, typical vulnerabilities are missing ownership checks, missing signer checks, signed invocation of unverified programs, Solana account confusions, missing freeze authority checks, insufficient SPL account verification, missing rent exemption assertion, casting truncation, arithmetic overflow/underflow, instructions account checks, rug pull mechanisms or hidden backdoor checks, outdated dependencies, none returned during any failure, unreferenced accounts checks, serialize and deserialize checks, account address checks, unaudited external dependencies, program upgrade checks, account mutable checks, etc.
Tokenomics: tokenomics is a term coined by combining the two words “token” and “economics”. It means the economics of a crypto token and it usually covers the issuance, functionality, objective, allocation policy, and more of the crypto token. These factors all together form the characteristics of the crypto token’s supply and demand. A good tokenomics makes a crypto token appeal to both investors and users. Therefore, the tokenomics of an application is vital to an application’s long-term development and success. For a blockchain game e.g., a play-to-earn game, its tokenomics plays a key role.
Vulnerabilities in tokenomics can usually be uncovered in the design of the rules and functionality of a crypto token. This is more from an economical point of view rather than a technical point of view. In general, an awful tokenomics lacks a mechanism to incentivize users or investors to buy and hold tokens.
Typical vulnerabilities pertaining to tokenomics from an economical point of view are lack of token utilities, unlimited token supply, lack of liquidity, etc.
Governance: a significant feature that a blockchain application has compared with a conventional web 2.0 application is that it has a governance mechanism with which its token holders can participate in its activities and make decisions in guiding its development by voting with the application’s token. Vulnerabilities in the governance usually are uncovered in its rules and voting mechanism.
Typical vulnerabilities in governance are including inappropriate voting rules, inappropriate staking rules, inappropriate snapshot rules, inappropriate proposal submission rules, etc.
In-Game Assets or Utilities: in-game assets or utilities are implemented by smart contracts as either fungible tokens or non-fungible tokens. They have utilities that can be used in games for specific purposes.
Vulnerabilities concerning in-game assets or utilities are those that cause the assets or utilities out of work. These vulnerabilities are usually uncovered in the functional design or logic design.
Typical vulnerabilities about in-game assets or utilities are implementation vulnerabilities, design vulnerabilities, functional vulnerabilities, etc.
Implementation of On-Chain Logic: this refers to the business logic of an application. Specifically, for a blockchain application, to make its rules and logic tamper-proof and censorship-resistant, the team behind the application would code some or all of its business rules or logic in smart contracts.
Popular on-chain logic that is implemented in smart contracts includes decentralized exchange rules, borrowing, and lending rules, staking rules, liquidity mining rules, NFT fractionalization rules, etc.
Typical vulnerabilities in the implementation of on-chain logic are using improper oracles, missing emergent withdrawal functions, inappropriate LP price algorithm, unsafe token transfer, excessive admin rights, hidden backdoors, risky contract upgrade/migration, implementation vulnerabilities, design vulnerabilities, etc.
Data Storage Solutions: for blockchain applications, a popular way to handle data storage is to use a decentralized solution to save data. These decentralized solutions in general are based on decentralized protocols such as IPFS, Arweave, etc.
A good data storage solution should be able to save data consistently and permanently. This is especially important for NFT projects which need to have long-term data availability and reliability for metadata.
Vulnerabilities in a data storage solution would cause data loss or data inconsistency. Typical vulnerabilities pertaining to data storage solutions are unreliable data storage, lack of data redundancy, lack of data consistency, unreliable data retrieval service, etc.
Other Solutions/Services: these will be solutions based on the protocols that may be introduced in the future. For now, no specific vulnerabilities are listed here for this.
4. Security Checkpoints That Should Be Covered for Each Kind of Application in the Ecosystem
4.1 Games
Specifically, a blockchain game is backed and supported by the technologies depicted in the following diagram:
The components represented by solid green blocks are the ones that Games must rely on. The components represented by transparent blocks are the ones that Games may optionally rely on.
From this diagram, we can see that the major technologies that a blockchain game directly relies on including UIs, Backend Services, Tokenomics, Governance, In-Game Assets or Utilities, Implementation of On-Chain Logic, and Data Storage Solutions. Optionally Other Decentralized Solutions may be relied on as well.
Consequently, the vulnerabilities we listed for each of the direct technologies and their underlying technologies in the previous section should be considered as the checkpoints for a blockchain game.
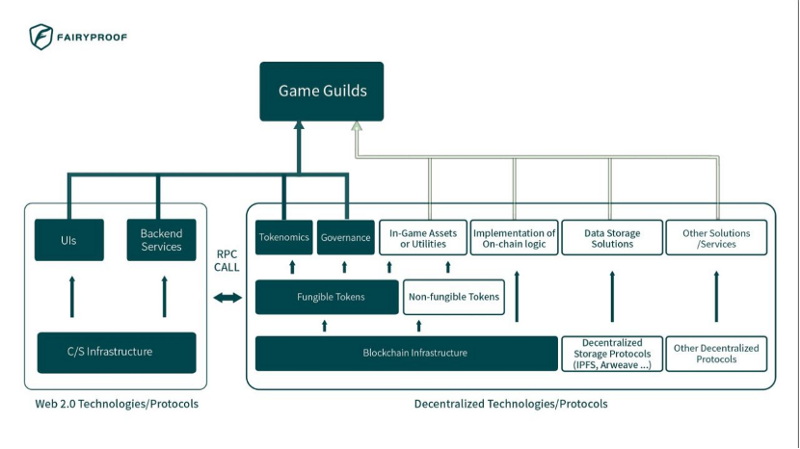
4.2 Game Guilds
Specifically, a blockchain game guild is backed and supported by the technologies depicted in the following diagram:
The components represented by solid green blocks are the ones that Game Guilds must rely on. The components represented by transparent blocks are the ones that Games may optionally rely on.
From this diagram, we can see that the major technologies that a blockchain game guild directly relies on upon including UIs, Backend Services, Tokenomics, and Governance. Optionally In-Game Assets or Utilities, Implementation of On-Chain Logic, Data Storage Solutions, and Other Decentralized Solutions may be relied on as well.
So, the vulnerabilities we listed for each of the direct technologies and their underlying technologies in the previous section should be considered as the checkpoints for a blockchain game guild.
4.3 Game Developers
Specifically, a blockchain game developer is backed and supported by the technologies depicted in the following diagram:
The components represented by solid green blocks are the ones that Game Developers must rely on. The components represented by transparent blocks are the ones that Games may optionally rely on.
From this diagram, we can see that the major technologies that a blockchain game developer directly relies on including UIs, Backend Services, Tokenomics, Governance, Implementation of On-Chain Logic, and Data Storage Solutions.Optionally In-Game Assets or Utilities and Other Decentralized Solutions may also be relied on.
So, the vulnerabilities we listed for each of the technologies and their underlying technologies in the previous section should be considered as the checkpoints for a blockchain game developer.
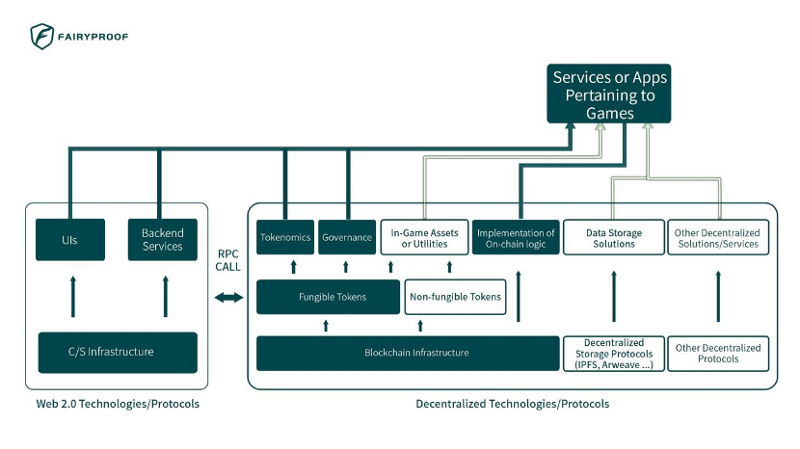
4.4 Services or Apps Pertaining to Games
Specifically, service or app pertaining to blockchain game(s) is backed and supported by the technologies depicted in the following diagram:
The components represented by solid green blocks are the ones that Services or Apps Pertaining to Games must rely on. The components represented by transparent blocks are the ones that Games may optionally rely on.
From this diagram, we can see that the major technologies that service or app pertaining to blockchain game(s) relies on upon including UIs, Backend Services, Tokenomics, Governance, and Implementation of On-Chain Logic. Optionally In-Game Assets or Utilities, Data Storage Solutions, and Other Decentralized Solutions may also be relied on.
So, the vulnerabilities we listed for each of the items in the previous section should be considered as the checkpoints for a service or app on blockchain game(s).
Conclusion:
In this paper, we explore the applications and technological modules of the existing blockchain GameFi ecosystem, list typical vulnerabilities of each of the technological modules and present our ideas on what specific areas we would study when we audit or check the security condition of an application in this ecosystem.
We are keeping our work and close attention to the GameFi ecosystem’s development and would always do our best to contribute to the ecosystem’s security and expansion.
References:
[1] CryptoKitties, https://www.cryptokitties.co/
[2] Axie Infinity, https://axieinfinity.com/
[3] YGG, https://yieldguild.io/
[4] Crypto VCs Are Making a Big Bet on Gaming Guilds. Why?
https://www.coindesk.com/markets/2021/12/21/crypto-vcs-are-making-a-big-bet-on-gaming-guilds-why/, December 27, 2021
[5] Decentralized autonomous organizations (DAOs), https://ethereum.org/en/dao/
[6] Sky Mavis, https://skymavis.com/, 2021
[7] Vulcan Verse, https://vv.vulcanforged.com/, 2022
[8] OpenSea, https://opensea.io/
[9] SkyMarvis’ Marketplace, https://marketplace.axieinfinity.com/
[10] NFTFI, https://www.nftfi.com/
[11] IPFS, https://ipfs.io/
[12] Arweave, https://www.arweave.org/
[13] ERC-20 Token Standard,
https://ethereum.org/en/developers/docs/standards/tokens/erc-20/
[14] Solana, https://solana.com/
[15] ERC-721 Non-fungible Token Standard,
https://ethereum.org/en/developers/docs/standards/tokens/erc-721/
[16] EIP-1155: Multi Token Standard, https://eips.ethereum.org/EIPS/eip-1155
About the author:
Yuefei TAN, CEO of Fairyproof
About Fairyproof:
Fairyproof Tech is a blockchain security company, established in Jan 2021.
It was founded by a team with rich experience in smart contract programming and network security. The team members participated in initiating several draft standards in the Ethereum field, including ERC-1646, ERC-2569, ERC-2794, and EIP-3712, of which ERC-2569 was officially accepted by the Ethereum team.
The team participated in the launch and development of various Ethereum projects, including blockchain platforms, DAO organizations, on-chain data storage, and decentralized exchanges, and conducted security audits of multiple projects which have been deployed on Ethereum. Based on its strong R&D capability and deep understanding of smart contract security, Fairyproof has developed comprehensive vulnerability tracking and security systems and tools.
Fairyproof Tech serves and works closely with customers by providing systematic solutions covering both “code vulnerabilities” and “logic vulnerabilities” and aims to provide customers with the best and most professional services.
Join Coinmonks Telegram Channel and Youtube Channel learn about crypto trading and investing