Review of Blockchain Security in 2023
For the Year 2023, Presented by Fairyproof in 2023
Executive Summary
The overall crypto market trended up dramatically through 2023 compared to 2022. And the attacks against the crypto ecosystem became more active with regard to the number of attacks in our statistics.
- Crypto assets worth around US $1.23 billion were exploited in 489 prominent security incidents.
- As the BTC ecosystem grew rapidly 13 prominent attacks were against it.
- The loss (US $517.5 million) caused by private keys leaked accounted for 45.07% of the total loss in the attacks from hackers. Safely and securely managing private keys should always be the Number 1 thing any crypto users should keep in mind.
- In 2023, Fairyproof had extensively researched the ZK(zero-knowledge proof [1]) related technologies and has been familiar with the existing mainstream solutions in the industry. Fairyproof has established its own development process and model, and can promptly deliver solutions based on application requirements. With regards to ZK-related audits, Fairyproof has rich experience and is proficient in converting a problem to ZK circuits, auditing circuits, proof generation, proof verification, and more. In addition, Fairyproof has been actively working on optimizing ZK-related implementation and improving its security such as using MPC technology to decentralize the initial setup in ZK-Snark implementations.
- In 2023, Fairyproof had established strong technical strength in MPC [2] related technologies and has established its own development process and model, and can promptly deliver solutions for popular applications such as using MPC to do omnichain transactions.
BACKGROUND
Before proceeding, the following terms and technologies are introduced in this report:
CCBS
CCBS stands for “Centralized Crypto or Blockchain Service”. A CCBS refers to a platform or service that provides crypto or blockchain related products or services, and is run by a conventional / centralized organization, entity or company such as conventional crypto exchanges (eg. Binance or Tether).
FLASHLOAN
Flash loans are a popular feature that hackers utilize when attacking EVM-Compatible smart contracts. Flash loans were developed by the team behind the famous DeFi application AAVE [3]. This feature “allows users to borrow any available amount of assets without putting up any collateral, as long as the liquidity is returned to the protocol within one block transaction” [4]. Flash loans are quite often used to borrow ERC-20 tokens [5] and attack DeFi applications. To initiate a flash loan, users will need to write a contract that borrows an available amount of assets and pay back the loan + interest + necessary fees all within the same transaction.
CROSS-CHAIN BRIDGE
A cross-chain bridge is an infrastructure that connects multiple independent blockchains and enables an exchange of cryptos, data or information from one blockchain to another.
As more blockchains have their own ecosystems, cryptos and dApps, the need for exchanging cryptos or data across different blockchains becomes increasingly high while the volume of cross-chain transactions dramatically increase. This causes cross-chain bridges to suffer more attacks.
FOCUS OF THIS REPORT
In this report we list our statistics collected from typical security incidents that happened in the blockchain space in 2023, give an in-depth analysis of their root causes, and present our recommended best practices.
STATISTICS AND ANALYSIS OF SECURITY INCIDENTS OF 2023
We studied 489 prominent security incidents that occurred in 2023 and present our statistics and analysis based on the targets and root causes.
In 2023 the total value of the exploited assets was US $1.23 billion and the overall market cap of the cryptocurrency according to Tradingview was US $1616 billion. The value of the exploited assets accounted for 0.08% of the total market cap of the cryptocurrency.
INCIDENTS CATEGORIZED BY TARGETS
Our researched incidents can be categorized into four types of targets:
1. CCBS
2. Blockchains
3. DApps
4. Cross-chain Bridges
A CCBS-related incident is one in which a centralized crypto or blockchain service platform is attacked by hackers resulting in the failure of its services or a loss of crypto assets under its custody.
A blockchain-related incident is one where a blockchain mainnet, side chain or layer 2 is attacked by malicious actors from inside, outside, or both, resulting in its operation going out of order, or that a blockchain fails to work properly due to issues related to software, hardware, or both. Attackers will then be able to exploit the consensus for profits.
A dApp-related incident is one where a dApp’s daily operation goes out-of-order or is attacked, leaving it open for attackers to exploit users and crypto assets under the custody of the dApp.
A cross-chain bridge-related incident occurs when a cross-chain bridge is attacked resulting in a loss of crypto assets under its custody or a failure of the exchange function between multiple blockchains.
There were 489 incidents in total. Here is a figure that shows the percentage for each of these targets respectively.
The number of dApp-related incidents account for more than 88.34% of the total incidents. Out of 489 incidents, 20 were CCBS-related, 26 were blockchain-related, none cross-chain bridge-related, and 432 were dApp-related.
BLOCKCHAIN-RELATED INCIDENTS
Incidents that had occurred in blockchains can be further categorized into three sub-categories:
i. Blockchain mainnets
ii. Side chains
iii. Layer 2 solutions
A blockchain mainnet, also known as layer 1, is an independent blockchain that has its own network with its own protocol,
consensus, and validators. A blockchain mainnet can validate transactions, data, and blocks generated in its network by its own validators and reach a finality. Bitccoin and Ethereum are typical blockchain mainnets.
A side chain is a separate, independent blockchain which runs in parallel to a blockchain mainnet. It has its own network consensus and validators. It is connected to a blockchain mainnet (eg. by a two-way peg [6]).
A layer 2 solution refers to a protocol or network that relies on a blockchain as its base layer (layer 1) for security and finality [7].
Its main purpose is to solve scalability issues of its base layer. It processes transactions faster and costs less resources compared to its base layer. Since 2021, there has been a huge surge in the growth and development of layer 2 solutions for the Ethereum ecosystem.
Both side chains and layer 2 solutions exist to solve the scalability issues of a blockchain mainnet. The significant difference between a side chain and a layer 2 solution is that a side chain does not necessarily rely on its blockchain mainnet for security or finality whereas a layer 2 solution does.
There were 26 blockchain-related incidents in total in 2023. The figure below shows the percentages of blockchain mainnet related incidents, side-chain related incidents, and layer 2 related incidents respectively.
The number of blockchain mainnet related incidents and layer 2 related incidents account for 84.62% (22) and 15.38% (4) of the total incidents respectively. No prominent side-chain related incidents were covered in our statistics. The attacked layer 2 solutions were Metis [8], zkLink [9], Boba [10] and Arbitrum [11]. Among the attacked blockchain mainnets, Mixin was one that suffered the most in crypto assets and others mostly just suffered social media attacks without significant loss.
DAPP RELATED INCIDENTS
Among the 432 incidents that occurred toward dApps, 45 were rug-pulls, 263 were involved in exploitations and 124 were directly attacked. An attack against a dApp can specifically target its front-end, server side, or smart contract(s). We can therefore further classify these 124 incidents into three sub-categories:
i. dApp’s front-end
ii. dApp’s server side
iii. dApp’s smart contract(s)
dApp’s front-end related incidents refer to events where vulnerabilities from the conventional client side are exploited, compromising on the account information and personal details of users which can be used to steal their crypto assets.
dApp’s server side related incidents are those where vulnerabilities present in the conventional server side are exploited, leaving on-chain and off-chain communication open for hijacking and crypto assets of users open for exploitation.
Smart contract related incidents refer to vulnerabilities in a smart contract’s design or implementation, which are leveraged to exploit crypto assets from users.
Here is a figure that shows the percentages of front-end, server-side and smart contract related incidents respectively.
The above figure shows the number of smart contract related incidents, server side related incidents, and front-end related incidents, accounting for 95.16%, 0%, and 4.84% of the total incidents respectively. Among 124 incidents, 6 were front-end related and 118 were smart contract related.
We further studied the amount of loss incurred from these sub-categories. Our study showed that the amount of loss in front-end related incidents was US $238,000, and the amount of loss in smart contract related incidents was US $541.75 million.
It is clear that smart contract related incidents were the biggest issue. Typical vulnerabilities we found pertaining to smart contracts in 2023 include logic vulnerabilities, private key leaks, flash loans, price manipulation, re-entrancy attacks, and more.
We studied the 118 incidents in which smart contracts were directly attacked and derived the following figure based on vulnerability types:
The figure shows that the number of incidents with the highest percentage was logic vulnerabilities and followed by flashloan attacks. Logic vulnerabilities mainly include missing validations for parameters, missing validation for access control, etc. 53 projects suffered from logic vulnerabilities and 28 suffered from flashloan attacks.
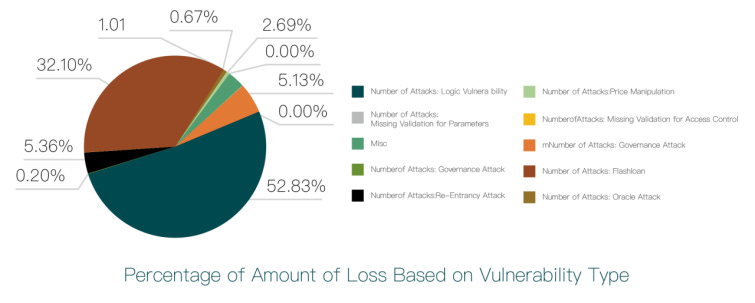
The following figure illustrates the amount of loss for each vulnerability type:
The amount of loss caused by logic vulnerabilities still ranked first. 53 incidents were caused by logic vulnerabilities, totaling a loss of US $286.19 million. This loss accounting for 52.83% of the total loss. The amount of loss caused by private key leaks ranked second. 6 incidents were caused by private key leaks, totaling a loss of US $173.92 million. This loss accounted for 32.1% of the total loss. Meanwhile, 10 incident caused by re-entrancy attacks totaled a loss of US $29.06 million and accounted for 5.36% of the total loss, ranking third.
INCIDENTS CATEGORIZED BY ROOT CAUSES
The root cause of these incidents can be categorized into the following:
i. Attacks from hackers
ii. Rug-pulls
iii. Misc.
We studied these incidents and got the following figure.
The above figure shows that the number of attacks from hackers and rug-pulls incidents accounted for 88.75% (434) and 9.2% (45) of the total incidents respectively.
We studied the amount of loss of each category of incidents based on the root cause and got the following figure:
The above figure shows that the amount of loss in the incidents that suffered from attacks and the amount of loss in rug-pull incidents each accounted for 93.04% and 3.87% of the total loss respectively. The amount of loss in the incidents that suffered from attacks was US $1.15 billion and the amount of loss in rug-pull incidents was US $47.76 million. This reveals that attacks from hackers posed the largest threat to the whole crypto ecosystem in 2023.
ATTACKS FROM HACKERS
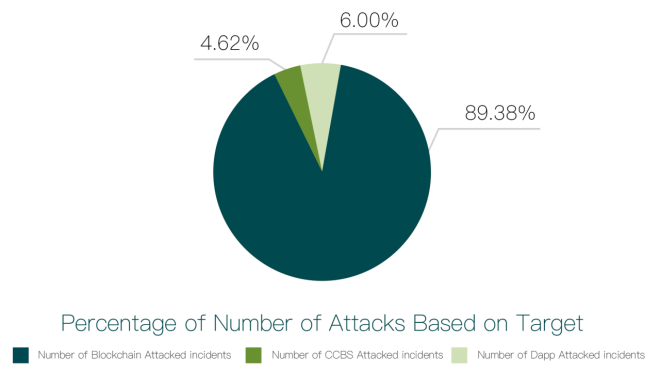
We studied the targets the hackers attacked and got the following figure:
The figure above shows that the number of attacks on dApps, CCBSs and blockchains accounted for 89.38% (387), 4.62% (20) and 6% (26) respectively.
After we studied the amount of loss in each of them we got the following figure:
The amount of loss in attacks on dApps, CCBSs and blockchains were 58.95%, 24.03% and 17.02%, resulting in a loss of US $693.58 million, US $282.72 million and US $200.19 million respectively.
RUG-PULLS
The rug-pulls that happened in 2023 were against dApps. There were 45 incidents totaling a loss of US $47.76 million which were not as severe as losses caused by attacks.
RESEARCH FINDINGS
dApps were the most prominent target for attacks in 2023 as the most number of attacks were against them. And the amount of loss caused by attacks on dApps also ranked first totaling a loss of US $693.58 million and accounting for 58.95% of the total loss that suffered from attacks from hackers. This reveals that the overall security situation of the existing dApps is a big concern for the whole crypto space.
Hackers proved to remain as the main threat to the crypto industry, accounting for more than 88.75% of all the number of incidents and more than 93.04% of the total loss. It far surpassed any other root causes such as rug-pulls, etc.
Both the number of attacks on layer 2 solutions and the amount of loss in these attacks decreased dramatically in 2023 compared to those of 2022. We think this was due to more attention paid to the security of layer 2 solutions and better maturity of layer 2 solutions.
A dApp consists of three parts: a front-end, a server-side and smart contracts. Either one or multiple parts are targeted during dApp attacks. According to our statistics, smart contract(s) accounted for an extraordinarily high percentage of attacks compared to the front-ends or server sides with regard to both attack frequencies and amount loss in 2023. This shows that attacks on smart contracts still posed as the biggest threat to dApps.
All of the rug-pulls in 2023 were dApps.
Finally, for smart contract related incidents, we find both the number of attacks and the loss caused in the attacks that rank first in 2023 was the attacks that exploited logic vulnerabilities. They surpassed any one of the other sub-categories.
TENTATIVE THOUGHTS
In addition, more project teams rushed to or planned to jump in Zero Knowledge (zk) related applications including zk-rollup solutions for Ethereum, zk related social applications, and more. We think there will be an increasing demand for audits of zk related applications.
BEST PRACTICES TO PREVENT SECURITY ISSUES
In this section we present some best practices to help both blockchain developers and users manage the risks posed by the incidents that happened in 2023, and support coordinated and efficient response to crypto security incidents. We would recommend both blockchain developers and users to apply these practices to the greatest extent possible based on the availability of their resources.
Note: “Blockchain developers” refers to both developers of blockchains and developers of dApps, and blockchains or systems pertaining to crypto cyrrencies. Here, “blockchain users” refer to everyone that participates in activities pertaining to crypto system’s management, operation, trading, etc.
FOR BLOCKCHAIN DEVELOPERS
Developers of cross-chain bridges need to pay closer attention to the bridges’ security as cross-chain transactions become increasingly popular. Cross-chain bridge solutions include handling of operations – not only on-chain but also off-chain. Naturally, the off-chain part would be more vulnerable to attacks. Hence, security solutions for cross-chain bridges should be particularly capable of handling off-chain activities safely and securely.
Awareness of security for layer 2 solutions should still be kept even though attacks on them were few with negligible losses as more layer 2 solutions will emerge in the coming years. Research and development for solutions to tackle security challenges in this area must be prompt.
A step to transfer an admin’s access control to a multi-sig wallet or a DAO to manage access control to crypto assets or critical operations is a must-have.
Attackers would employ flash loans to maximize their exploits when they detect vulnerabilities in smart contracts, including issues of re-entrancy, missing validations for access control, incorrect token price algorithm, and more. Proper handling of these issues should have the highest priority for a smart contract developer when designing and coding a smart contract.
Our statistics show that an increasing number of hackers have been using social media tools – especially Discord – to launch phishing attacks. This persisted through the whole year of 2023 and will very likely persist in 2024. Many users have suffered huge losses. Project developers and managers are advised to prioritize safely and securely managing social media accounts and finding security solutions for them on top of project implementation.
FOR BLOCKCHAIN USERS
More users are varying their crypto portfolio across different blockchains. The demand for cross-chain transactions is rapidly increasing. Whenever a user participates in a cross-chain transaction, the user will have to interact with a cross-chain bridge – a popular target among hackers. Hence, before starting a cross-chain transaction, users are advised to investigate the bridge’s security condition and ensure they use a reliable, safe and secure bridge.
While it is necessary to pay great attention to the security for smart contracts when interacting with a dApp, the importance to also pay attention to the security of the user interface while exercising caution to detect suspicious messages, prompts, and behavior presented by the UI is increasing.
We strongly urge users to check whether a project has audit reports and read these reports before proceeding with further actions.
Use a cold wallet or a mutl-sig wallet where possible to manage crypto assets that are not for frequent trading. Be careful about using a hot wallet and make sure the hardware in which a hot wallet is installed is safe and secure.
Be cautious of a dApp where its team members are unknown or lack reputation. Such dApps may eventually be rug-pull projects.
Be cautious of a centralized exchange which has not established a reputation or does not have tracked transaction data on third party media as it may also eventually prove to be rug-pull projects.
REFERENCES
[1] zero-knowledge proof. https://en.wikipedia.org/wiki/Zero-knowledge_proof
[2] MPC. https://en.wikipedia.org/wiki/Secure_multi-party_computation
[3] Aave. https://aave.com/
[4] Flash-loans.. https://aave.com/flash-loans/
[5] ERC-20 TOKEN STANDARD. https://ethereum.org/en/developers/docs/standards/tokens/erc-20/
[6] Sidechains. https://ethereum.org/en/developers/docs/scaling/sidechains/
[7] Layer-2. https://academy.binance.com/en/glossary/layer-2
[8] Metis. https://www.metis.io/
[9] zkLink. https://zk.link/
[10] Boba. https://boba.network/
[11] Arbitrum. https://arbitrum.io/